 Chapter 5 of Partners for Preservation [1] is ‘The Internet of Things: the risks and impacts of ubiquitous computing’ by Éireann Leverett [2]. This is one of the chapters that evolved a bit from my original idea – shifting from being primarily about proprietary hardware to focusing on the Internet of Things (IoT) and the cascade of social and technical fallout that needs to be considered.
Chapter 5 of Partners for Preservation [1] is ‘The Internet of Things: the risks and impacts of ubiquitous computing’ by Éireann Leverett [2]. This is one of the chapters that evolved a bit from my original idea – shifting from being primarily about proprietary hardware to focusing on the Internet of Things (IoT) and the cascade of social and technical fallout that needs to be considered.
Leverett gives this most basic definition of IoT in his chapter:
At its core, the Internet of Things is ‘ubiquitous computing’, tiny computers everywhere – outdoors, at work in the countryside, at use in the city, floating on the sea, or in the sky – for all kinds of real world purposes.
In 2013, I attended a session at The Memory of the World in the Digital Age: Digitization and Preservation [3] conference on the preservation of scientific data [4]. I was particularly taken with The Global Sea Level Observing System (GLOSS) [5] — almost 300 tide gauge stations around the world making up a web of sea level observation sensors. The UNESCO Intergovernmental Oceanographic Commission (IOC) established this network, but cannot add to or maintain it themselves. The success of GLOSS [6] “depends on the voluntary participation of countries and national bodies”. It is a great example of what a network of sensors deployed en masse by multiple parties can do – especially when trying to achieve more than a single individual or organization can on its own.
Much of IoT is not implemented for the greater good, but rather to further commercial aims. This chapter gives a good overview of the basics of IoT and considers a broad array of issues related to it including privacy, proprietary technology, and big data. It is also the perfect chapter to begin Part II: The physical world: objects, art, and architecture – shifting to a topic in which the physical world outside of the computer demands consideration.
Bio:
Éireann Leverett [2] once found 10,000 vulnerable industrial systems on the internet.
He then worked with Computer Emergency Response Teams around the world for cyber risk reduction.
He likes teaching the basics and learning the obscure.
He continually studies computer science, cryptography, networks, information theory, economics, and magic history.
He is a regular speaker at computer security conferences such as FIRST, BlackHat, Defcon, Brucon, Hack.lu, RSA, and CCC; and also at insurance and risk conferences such as Society of Information Risk Analysts, Onshore Energy Conference, International Association of Engineering Insurers, International Risk Governance Council, and the Reinsurance Association of America. He has been featured by the BBC, The Washington Post, The Chicago Tribune, The Register, The Christian Science Monitor, Popular Mechanics, and Wired magazine.
He is a former penetration tester from IOActive, and was part of a multidisciplinary team that built the first cyber risk models for insurance with Cambridge University Centre for Risk Studies and RMS.
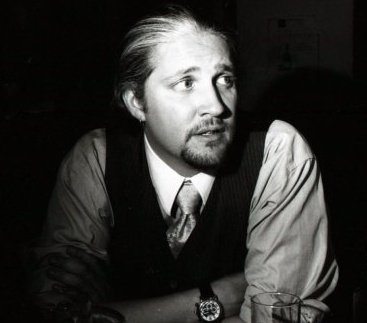
Image credit: Zan Zig performing with rabbit and roses, including hat trick and levitation [7], Strobridge Litho. Co., c1899.
NOTE: I chose the magician in the image above for two reasons:
- because IoT can seem like magic
- because the author of this chapter is a fan of magic and magic history
Comments Disabled To "Chapter 5: The Internet of Things: the risks and impacts of ubiquitous computing by Éireann Leverett"
#1 Pingback By Chapter 8: Preparing and Releasing Official Statistical Data by Professor Natalie Shlomo – Spellbound Blog On January 26, 2019 @ 3:16 am
[…] Almost eighty years ago, the woman in the photo above used a keypunch to tabulate the US Census. The amount of hands-on detail labor required to gather that data boggles the mind in comparison to born-digital data collection techniques now possible. The 1940 census was released in 2012 and is available online for free through a National Archives website. As archives face the onslaught of born-digital data tied to individuals, the techniques used by statisticians will need to become a familiar tool for archivists seeking to both increase access to data while respecting the privacy of those who might be identified through unfettered access to the data. This chapter serves as a solid introduction to SDL, as well as a look forward to new ideas in the field. It also ties back to topics in Chapter 2: Curbing The Online Assimilation Of Personal Information and Chapter 5: The Internet Of Things. […]
#2 Pingback By Overview of Partners for Preservation – Spellbound Blog On January 29, 2019 @ 2:41 am
[…] The Internet of Things: the Risks and impacts of Ubiquitous Computing by Éireann Leverett […]